I did test the same ransomware against a normal release and everything is fine the ransomware is contained and no damage so Xcitium Staff please fix bugs with containment
I use the beta version on my machine. Will I have to remove and install the old version?
Or will they fix it and release an update as soon as possible?
I hope Xcitium does release an bug fix with containment
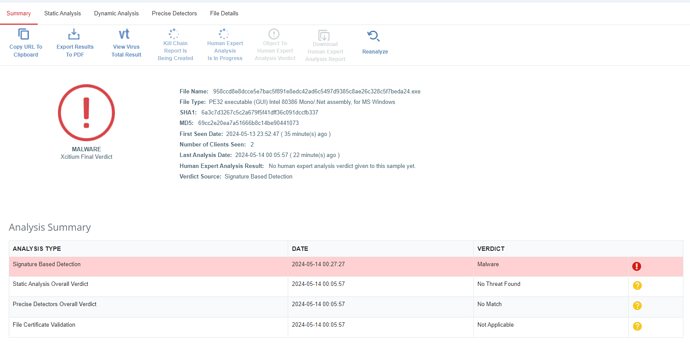
While the cash ransomware was contained Xcitium rated it as Malicious
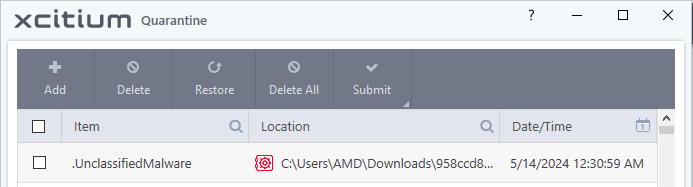
.UnclassifiedMalware@1
This is the same sample CIS 2024 got attacked by but it will be fixed
@Nik123 Does the test identify which ransomware cracks the protection? As I found the tester did an exclusion operation via the viruscope alert window. You can check the timeline starting at 11:16 in that video.
Configuration Internet Security 2 in video indicates altered configuration.
Do not virtualize folders which is defaulted to shared spaces and downloads folder is ticked.
Containment set to ignore desktop websites folder
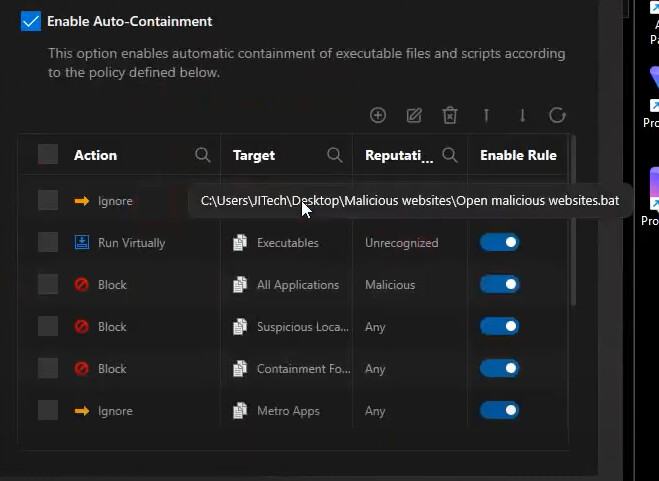
Actions not taken to remove malware and Container not reset after tests. I don’t have time to delve into it further at the moment but I believe results incorrect or items whitelisted.
Now, we have to know if the problem is with the containment or the test was done wrong.
Yes VirusScope detected the malware script so the guy clicked ignore and add to exclusions so it means that the malware is added to exclusions
Hi squareas,
Thank you for reporting.
As the current CIS is the beta version, comodo secure shopping were not included in this version.
Once the final CIS releases, CSS will be added.
For time being kindly download CSS from the below link.
Thanks
C.O.M.O.D.O RT
Indeed. If there was an issue with containment @cruelsister CruelSister YT Page would be the first to highlight it. As soon as you start turning off features and whitlisting folders and files, that weakens the security.
I noticed this exactly too, I was just about to write about it.
It is also worth unchecking the option in CIS - Do not virtualize access to (specific files and folders)
I don’t know why you specifically mention the Xcitium product.
I don’t see the enterprise version being tested.
Start using the Comodo Internet Security nomenclature.
Thanks but no i call it Xcitium/Comodo
Exeactly.
Xcitium/Comodo is one of the best vendor on unknown malware it does the job its supposed to do
so this test is unfair
he could of clicked Ignore Once and malware would be sandboxed and no damage would be done
@EricCryptid also i tested the same ransomware cash ransomware and it was contained
it didnt take like 20 minutes and Xcitium rated it as Malicious while it was contained
A couple of them try, but Comodo users sit back and drink coffee.![]()
Everyone else “ONLY detects bad files” ONLY and ONLY if they detect it.
We do Detection properly.
We detect not only “bad files”
we also detect "Unknown Files
and “Good files”
And if we detect “unknown files” we don’t risk and run it in containment while the user is using it.
An important point as Comodo will prevent true zero-day files that are also validly Signed AND Counter-signed from running (they will be classes as Unrecognized and thus contained).
All other anti-malware products would be oblivious to them, thereby exposing the system to be trashed or have personal data stolen (examples would be the first Magniber ransomware released to the Wild, and the Efile data stealer).
This is a strength of Comodo of extreme importance that is far too often ignored.
100% think it was just a poor test due to bad setting’s.
I wonder why there are many people who ignore this strong point of comfort. ![]()
They don’t want to admit it.