I tested CCE today on XP SP3 32 bits today with app. 100 zeroday malware.
No AV installed.
XP FW enabled.
KillSwitch replacing task manager.
After running all the malware (40 already downloaded malware & app. 60 malware were directly run through browser i.e pasting malware links in the browser.
Malware sources - MDL, MBL, Malc0de & CleanMX.
So after running all the malware I restarted the system. I was not able to run/open anything like msconfig, internet explorer, comodo dragon, security center, 7 zip, hitmanpro, malwarebytes, etc.
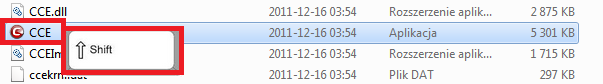
So I tried to open KillSwitch by right clicking in the taskbar, by going into the CCE folder in the system, usiing a USB which also had CCE installation, but I was not able to run KillSwitch, CCE Scan & Autorun with any way.
I was only able to open KillSwicth with Ctrl + Del & through KillSwicth I was able to open AutoRun & Quick Repair. After killing malware processes & repairing through quick repair & deleting malware entries through autorun I was able to run CCE scan too. After cleaning all the found malware by CCE scan the system was back to normal & everything was back to normal again.
Only 1 Question.
I was able to open KillSwitch only through Ctrl + Del & no other way, neither through USB. Once KillSwitch opened everything was good to go.
But what would have happened if I haven’t replcaed task manager with KillSwicth, I guess thats why KillSwicth opened with Ctrl + Del, right?
How would I have opened KillSwitch & perform the cleanup?