hello everybody…Im just wondering if anybody could help me with a little problem i have…i use firefox as my browser and only use firefox…Im just wondering if its possible to disable internet explorer in any way.? any help would be very much appreciated…thank you. :ilovecomodo:
Uninstalling IE has becomed very difficult if not impossible after IE6/Windows 2000 (Before, IEradicator and Revenge of Mozilla are fine).
The standard Microsoft removing tool only reverts to the precedent version and wipes the IE icon.
You could use radical ways (manually deleting it) or more sophisticated ones (using the registry without the help of any software, or gui running XPLite, option only working in full version).
Altough some people advocate for replacing windows explorer with a proprietary explorer, you would however run in most serious trouble even for browsing your local folders without any connexion whatsoever.
So, i guess that you only want to disable it:
Set your firewall to proactive, custom, and add a rule specifying the path for IE: block TCP and UDP.
Now, you can’t connect anymore.
Set to ask if some of your **** applications only work through IE (some security software updates do that…)
If you want to go further, set defense+ to paranoid: block and remember whatever you are asked for, including scvhost, com and dns requests…
I would not recommend removing IE because it is tied into the system and it starts
when windows start.
One more thing to keep internet explorer is when you have problem updating CIS
AV(or any other program update like Malwarebytes…) database is to enable-disable
work offline mode.
One of the workarounds for internet connections problems and so on.
Use custom policy mode for CIS firewall to treat IE as a blocked application.
And you can set Firefox to be the default internet browser.
I have removed every ability for IE to run under Comodo and used Auto Runs to remove its rights to run nevertheless it keeps on working and downloading several MB of files each day.
~Maxx~
I guess you have some trusted rule for IE.
Blocking it in the firewall does not keep it to launch, but definitely makes it unable to connect to any site.
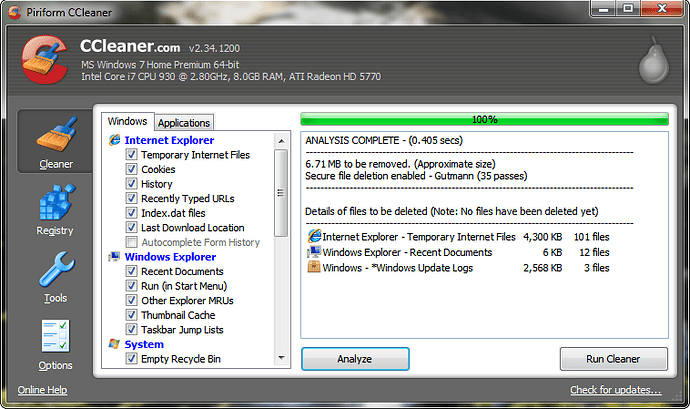
brucine- This is just a small example of IE downloading a few files, but I will make another screenshot when I am able to show you the 2-3 MB of download history files that IE generates nearly every day even though it has Blocked Application status in the Comodo Firewall. Hopfully you will be able to help me put an end to this behavior.
~Maxx~
[attachment deleted by admin]
I have the following configuration:
xp sp3 pro
cis v3, proactive
firewall in custom mode, alerts level is maximum, everything checked but ics
defense+ in paranoid mode, everything checked.
No trusted vendor.
Let’s write in the firewall the following rule:
http://brucine.hostoi.com/online/ie8.jpg
And now let’s launch IE to whatever url.
Let’s assume i allow all of the defense+ interventions:
http://brucine.hostoi.com/online/ie1.jpg
http://brucine.hostoi.com/online/ie2.jpg
http://brucine.hostoi.com/online/ie3.jpg
http://brucine.hostoi.com/online/ie4.jpg
http://brucine.hostoi.com/online/ie5.jpg
http://brucine.hostoi.com/online/ie6.jpg
Doing so, everything behaves as if defense+ was disabled (i allowed everything).
Now, the firewall takes the relay, interprets my rule, and ie is unable to connect to a working site (if not, i wouldn’t be writing):
brucine- Thank you for the demonstration that the initiation of IE outbound traffic can be prevented using the Comodo Firewall. Do you have any suggestions for how to prevent Microsoft from using IE to download 3-4 MB of files into my computer each day?
~Maxx~
In the stated “demonstration”, the firewall also blocks inbound connexions.
I guess that (i didn’t try it) blocking dns in defense+ for IE wouldn’t bring much.
The reason in my opinion of such a behavior is that some IE connexions actually don’t use directly iexplore.exe, and that cis is dumb enough to rely on executables name and path.
An obvious example of such a situation is OE: it uses the IE engine, no IE, no OE mail, yet you never see IE launched when you retrieve mail (actually downloading something).
It is also most probably the case with your screenshot showing that the culprit is Windows Update (and thus wuauclt.exe and not iexplore.exe).
Speaking of Windows Update, it uses an ActiveX ocx control, a definitely IE proprietary format, hence making in theory impossible to use it outside IE, altough you still can do it manually with Firefox as per:
http://mozillalinks.org/wp/2007/04/update-windows-within-firefox/
But of course, it won’t keep other lousy written software to want to connect through IE; as far as i remember, such a situation prevails with numerous softwares, including cis updates (i have them unchecked) and not either directly opening IE, and then you are stucked if you don’t find the mechanism.
It could be due to your files option behavior.
If opening them, and altough Firefox is your default browser, you shall observe that numerous file formats point to IE (jpg, ftp, shtml…) and you could want to correct that.
But you shall also observe that some items, e.g. Internet Shortcut, do not point to IE but use a peculiar syntax:
rundll32.exe shdocvw.dll,OpenURL %l
The culprit is therefore not IE, but rundll32.exe launching a dll.
Agressive rules in defense+ for monitoring rundll32.exe as an application and for monitoring dll (image execution set to agressive, adding dll) might overcome this behavior, but are not very convenient.
set security level to high
use iespyad for zonealarm
also repairIE ie has lots of options to restrict ie
hope that helps
I don’t think so, really, but you could try what you say and report us the result.
Outside of Windows Update (by definition using IE altough Microsoft was prosecuted for binding IE with Windows, it should therefore definitely not), the issue, as i said, is not IE itself:
blocked by a simple firewall rule, it doesn’t connect either inbound or outbound: period.
The problem results from other software loading IE stacks without running iexplorer.exe itself.
In this regard, it is always possible (xp) to set Temporary Files size to 1MB, wipe on exit, but not to zero, and to enforce some IE privacy options without even using any third-party software.
But not to forbid a third-party software to use IE “in your back”, unless probably fine settings in autoruns process by trial and error (peculiarly shell dlls), but it’s a lot of (dangerous) work, as it could lead you to be thrown out of some of your usual softwares and even from local browsing.
As i said before, some programs are speficillay written for their online help or update features to run only IE, and even if this behavior was overcomed by your local settings, you would not be able to change the software and/or its server themselves.
I don’t remember if the said programs are CIS “transparent”, or can enforce some kind of new defense+ rule: my choice, as memory serves, is the first option as, again, not ie but system exe (rundll32) and dll are involved, and that almost nobody, for usability reasons, sets defense+ in agressive image execution behavior monitoring dll.
This means that, in the event of totally blocking IE, you must not only manually use Windows Update, but make an appropriate choice of softwares never calling IE and also disable/unisnstall other ones, both Windows (Outlook Express…) and third-party.
Resuming what i said previously, there are 3 options.
-
Your software uses iexplorer.exe, connecting to a specific url
If you write a firewall IE blocking rule, you won’t even be able to connect, and nothing shall be downloaded.
Period. -
Your software has programmed settings writing to TIF.
It does not mean that IE is used, but only that the data is written there so as to be used afterwards by this software offline browsing.
No solution i can think of:
-internet zone security settings won’t stop such a behavior
-ntfs windows settings probably would (i don’t know, i’m running FAT32): set appropriate rights to the TIF folder?
-maybe forbidding windows offline browsing would, but of course very unconvenient
-finding from autoruns and disabling the concerned services also most probably would, but it’s a lot of trial and error testing.
-No straightforward way to block TIF writing from cis: setting TIF as a protected folder is not enough. -
Your software connects from its own executable, hardcoded to run through windows ie system applications (rundll32) and dlls and/or (see point 2) to download files from its own executable to TIF.
A good example is Offline Explorer (Offline Explorer - Free download and software reviews - CNET Download)
It’s an offline browser with a curious feature: it also allows browsing local files instead of using for that your favorite browser.
As soon as i launch it, it connects to localhost (http://127.0.0.1:800) and writes some files to TIF.
If i now use it to retrieve whatever internet site, it downloads the said file not only to the folder you specified, but also to TIF.
You are never prompted in any of these instances by the IE firewall rule, but by the firewall asking you to allow oe.exe and defense+ asking for control of afd device, windows sockets and dns.
If you deny, of course nothing is written.
But the culprit software is not IE but oe.exe.
No other solution but to individually deny whatever connecting in these conditions, but it would, in the said circumstances, make the software usability void.
If you don’t want whatever to be written to TIF (altough TIF is wiped when closing, limited in size, and set so that IE is not able to start or to run any script, thus making the threat very theoric), use other softwares…
Excepting this deliberate test, and remembering i don’t use windows update, i have nothing ever written to TIF: because i never use any software able to do so, meaning that the “solution” pertains to the softwares you are actually using.
Last, and outside cis and ie itself, a simple manipulation maybe would succeed:
Go to X:\Documents and Settings\UserName\Cookies, and set index.dat properties as read only.
Works under XP, if your OS does not want it, boot in safe mode and command line:
attrib +r (index.dat path)
brucine- Thanks for all of your helpful suggestions! I will refer back to this thread as I try to figure this out.
~Maxx~